Researchers have discovered Wi-Fi weaknesses that allow an attacker already connected to a wireless network to intercept traffic and set up attacks by exploiting inherent insecurities in the networking stack. Dubbed AirSnitch, this vulnerability allows the attacker to assume the identity of another legitimate device to confuse the network into diverting traffic through it, potentially enabling advanced cyberattacks.
The flaw was discovered by a research team from the University of California, which revealed multiple weaknesses of the existing Wi-Fi security stack. According to these findings, a malicious attacker could intercept data on a network that they already have access to, even when client isolation is active, which is supposed to prevent one client from targeting another. The attacker can be on the same SSID, a separate one, or even a separate network segment tied to the same access point or router.
While this is not as severe as a remote exploit since the attacker needs to be connected to the network to begin with, sharing your Wi-Fi with friends or neighbours, including guest networks, and you open up a potential security hole in your home network. Worse still, some ISPs deploy routers that broadcast secondary public Wi-Fi SSIDs in addition to the subscriber’s private home network as part of a shared-access program, which opens the door for anyone to enter your ‘guest’ network. The situation is exacerbated by public spaces and free Wi-Fi hotspots.
The research paper splits this bypass method into four main techniques. The first relies on shared/group keys, which opens a venue for an attack to craft packets intended for a specific victim. These can then be packaged inside frames that appear to be valid broadcast traffic. The second technique, called gateway bouncing, uses the router as a middle step to send traffic data to another device instead of a direct transmission to the victim, which would otherwise be blocked by client isolation.
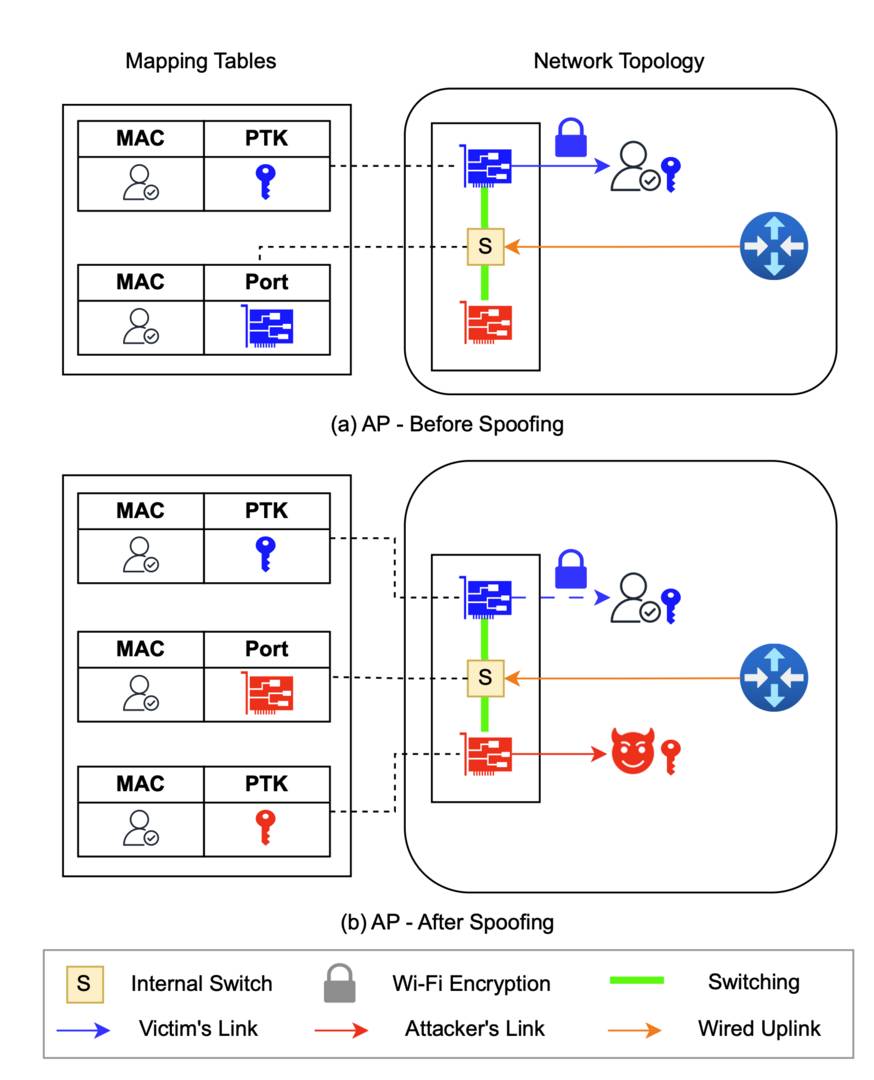
The last two involve MAC spoofing, where the attacker changes its hardware (MAC) address, pretending to be another device on the network. As a result, all data meant for that legit machine is diverted to the attacker. This works the other way around too, where the attacker can imitate the gateway and intercept traffic. The bigger issue is that this vulnerability has the potential of enabling advanced cyberattacks by combining it with other methods, such as cookie stealing or DNS and cache poisoning.
“This research shows that a wireless-connected attacker can subvert client isolation and implement full relay attacks against other clients, similar to old-school ARP spoofing. In a lot of ways, this restores the attack surface that was present before client isolation became common,” said HD Moore, a security expert and the founder and CEO of runZero.
The researchers discovered that at least one of these vulnerabilities is present in each of the 11 routers they tested. These include units from Netgear, D-Link, Ubiquiti, Cisco, plus others based on the DD-WRT firmware and the OpenWrt open-source router operating system. In other words, this is an architectural issue, not a vendor-specific bug.
The good news is that, according to the researchers who discovered this exploit, this type of attack remains complicated, especially on modern wireless networks. So, unless someone is targeting you specifically, you shouldn’t worry too much about it.